Microsoft Azure had an incident on 11/20, which its Front Door service got a bad deployment and blown-up Office 365, Bing, Azure DevOps, etc. Microsoft engineers very quickly fixed the issue. But Azure Front Door caught my eye, it is new to me. So, I took a look.
Azure Front Door
Typically, when we deploy our web applications to Azure App Service or other clouds, the network flow of a user visiting your site is very straight forward, the user's computer just sends the request directly to your server and get the response, this will have some potential issues.
First, the access speed. For example, my blog is deployed in East Asia, this makes users in the US visiting my site to have much slower speed than users in China. For static resources, I've already added Azure CDN to improve the performance, but CDN can't solve everything. Datacenters that are physically near the end-user certainly have a huge advantage in access speed. This is one of Azure Front Door's capability to automatically select the most nearby data center that runs your workload for the user.
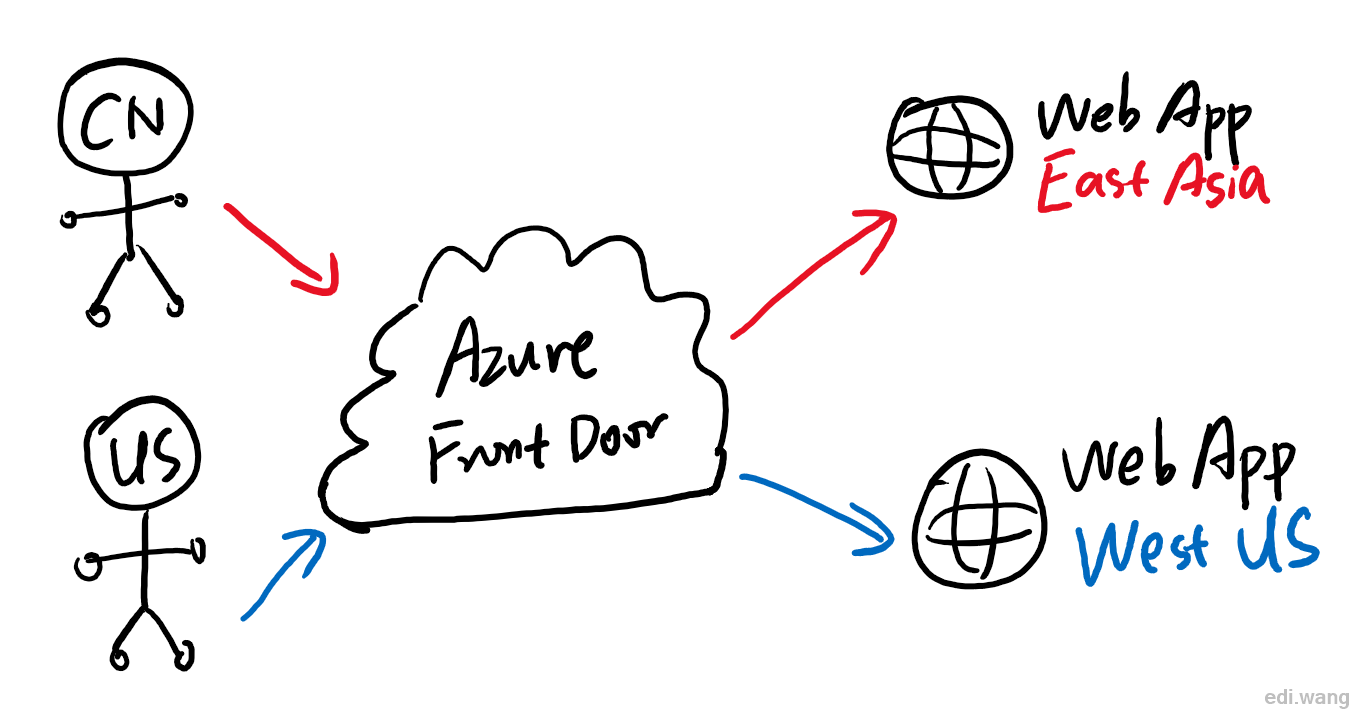
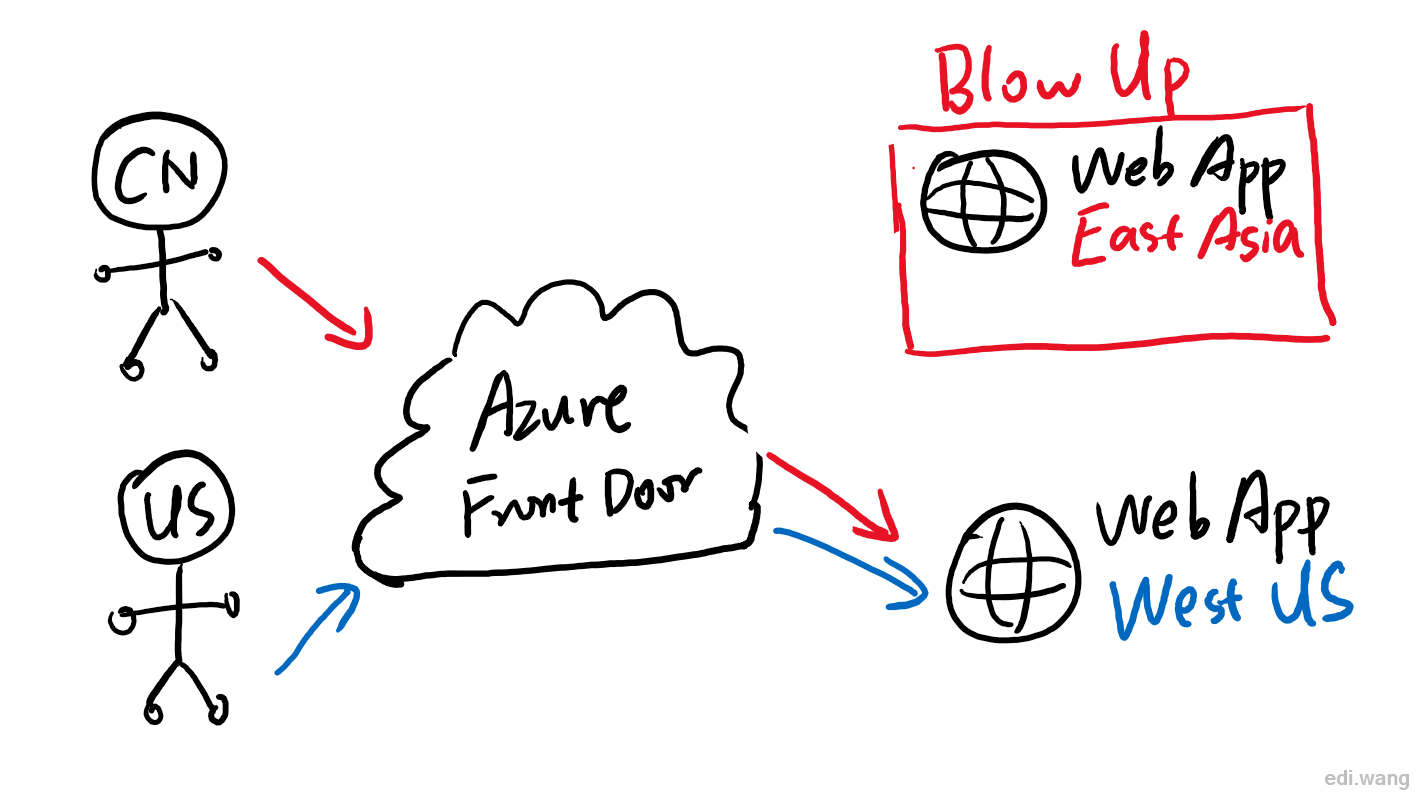
Second, it is about resilient. When your web site goes boom in a data center, or the datacenter itself goes boom. Azure Front Door can detect the failure and automatically route your users to the next nearby data center within minutes. The user will only notice a slower access speed rather than see your website blow up in front of the screen.
Another issue is security. Hackers and automated scripts can scan your site for security holes such as SQL injection, XSS and attack your site. The WAF comes with Azure Front Door can identify and stop these attacks, including request rate limit or block a region/country's entire IP address from accessing your site.
Usage Sample
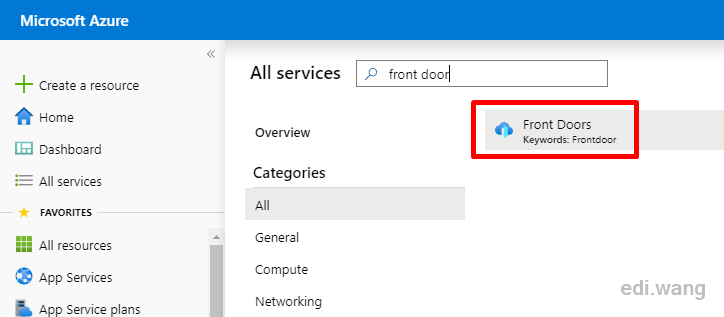
First, you can find and create a Front Door service in Azure Portal.
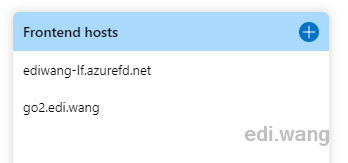
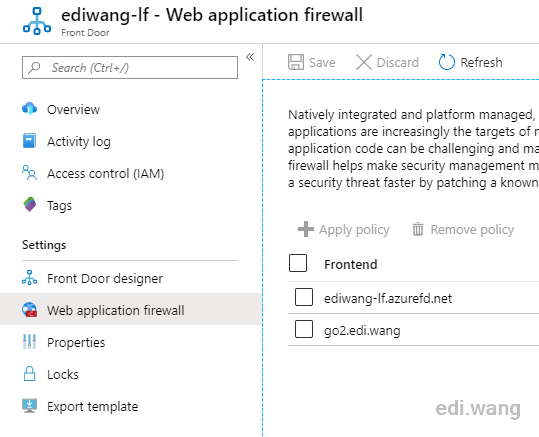
The "Frontend hosts" are where the user access entry point is. You'll need to create an address like <name>.azurefd.net, and you can add your own domain later. For example, your website used to use "https://996.icu", now you added a front door for it named "https://996icu.azurefd.net", after that, you can add 996.icu as an apex domain for 996icu.azurefd.net. Users will still be able to use your site with the same domain without noticing you've added the front door. In my example, I added a CNAME for go2.edi.wang
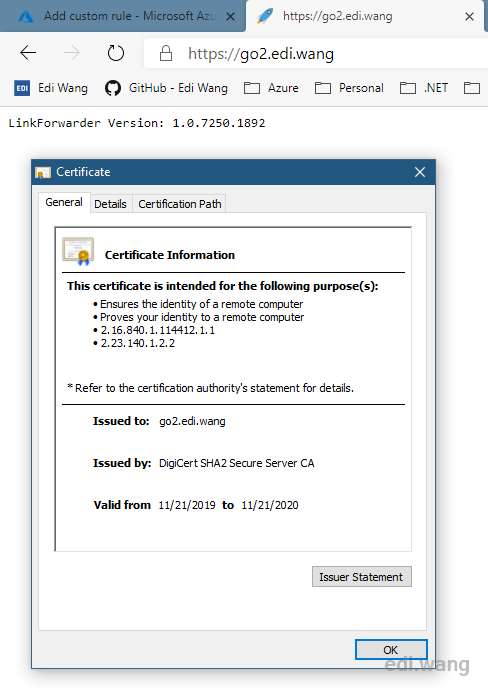
Azure gave me a free SSL certificate for this:
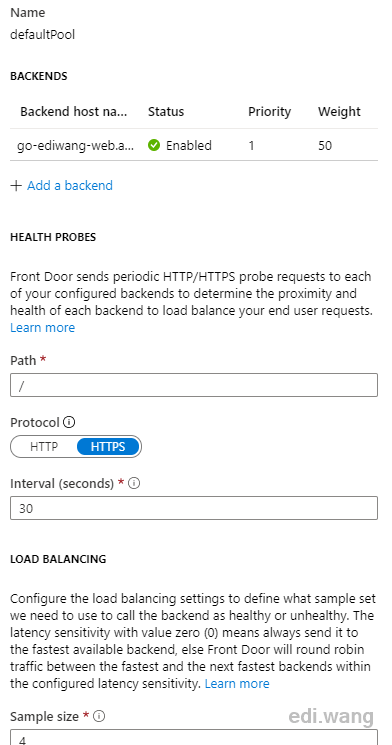
"Backend pools" means your backend servers. You can choose App Services, Storage Accounts, Cloud Services, that with an HTTP/S endpoint on Azure, or you can add your servers in another cloud or your own data center, it doesn't matter.
Because I only have one instance in one data center in my Azure subscription for my workload, so I configured only one backend host in the following screenshot. If you have multiple servers across multiple regions, you can take advantage of its load balancing feature.
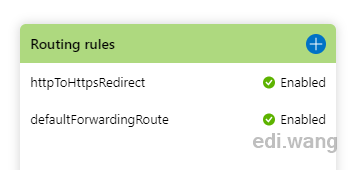
For the routing rules, you can configure them as you wish.
You can find Web application firewall in the menu, and create one or more policies for each entry point.
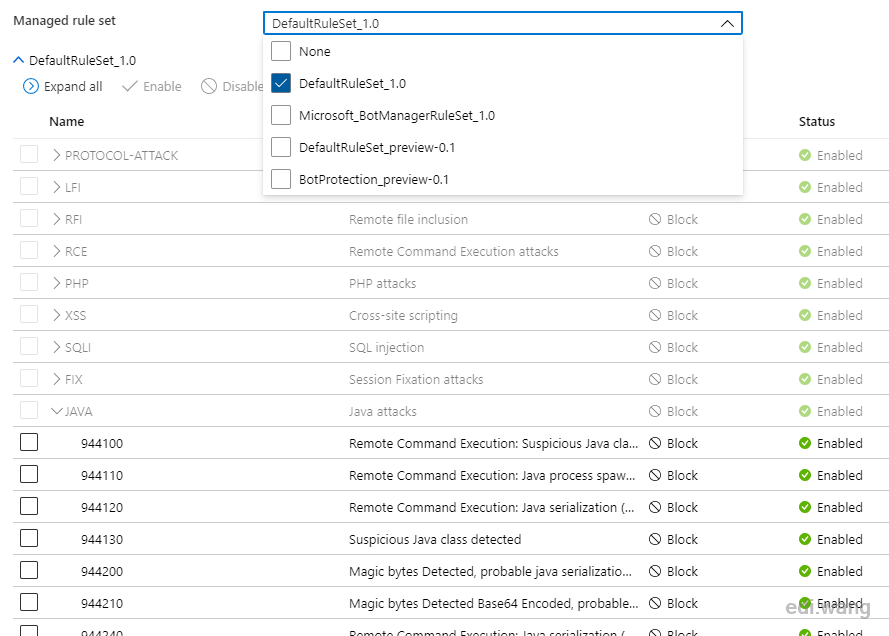
There are some pre-defined rules against the OWASP, such as preventing XSS, SQL Injection, common PHP and JAVA attacks.
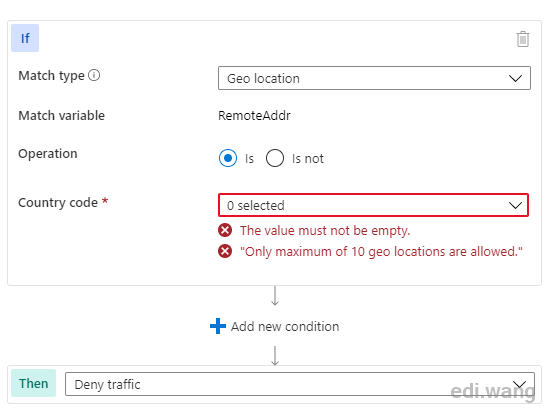
Of course, you can add your own. Such as blocking some regions' IP.
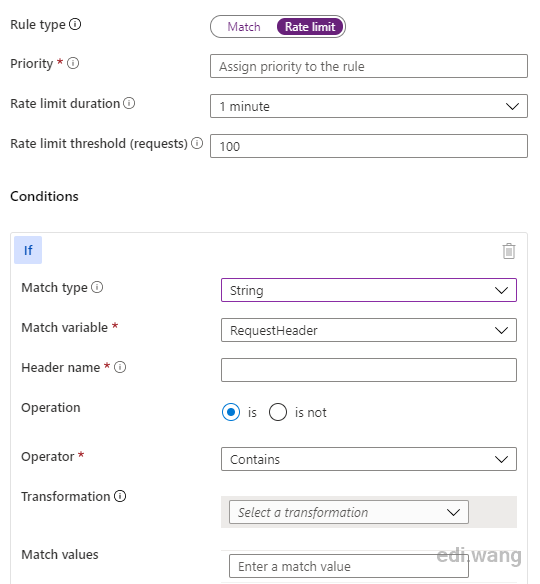
Or configure request rate limit without any change to your application code.
To learn more, please see Microsoft document for Azure Front Door
Comments