In my previous posts, I have introduced usage of Azure Front Door. However, when we finish setting up the front door and bind our domain to the front door, users can still access the App Service URL. In this post, I'll introduce how to prevent access to our App Service when using Azure Front Door.
Problem
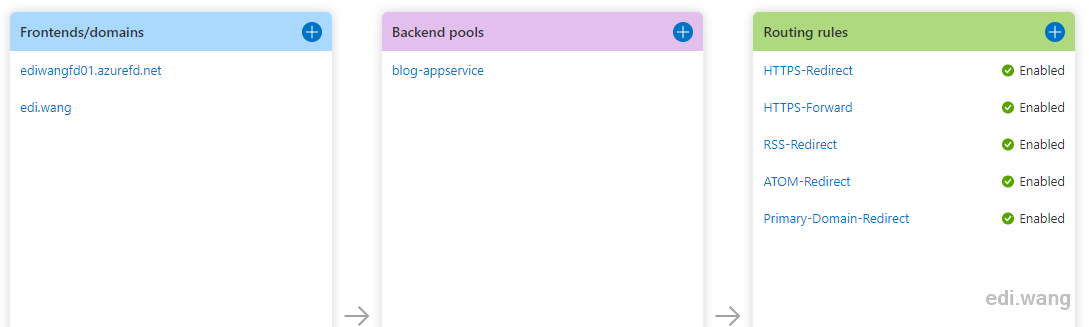
For example, my blog is binding https://edi.wang to my front door, I have 2 App Services running in backend pools in East Asia and West US. Their URLs are https://ediwang-web-ea.azurewebsites.net/ and https://ediwang-web-us.azurewebsites.net/. Normally, users visit my blog via https://edi.wang, which is powered by Azure Front Door and protected by Azure WAF. But in Azure Application Insights log, I can still see a few requests going for the raw App Service URLs. It can be dangerous because they are not protected by WAF.
Thus, I need to make App Service reject traffic that is not coming from Azure Front Door.
Solution
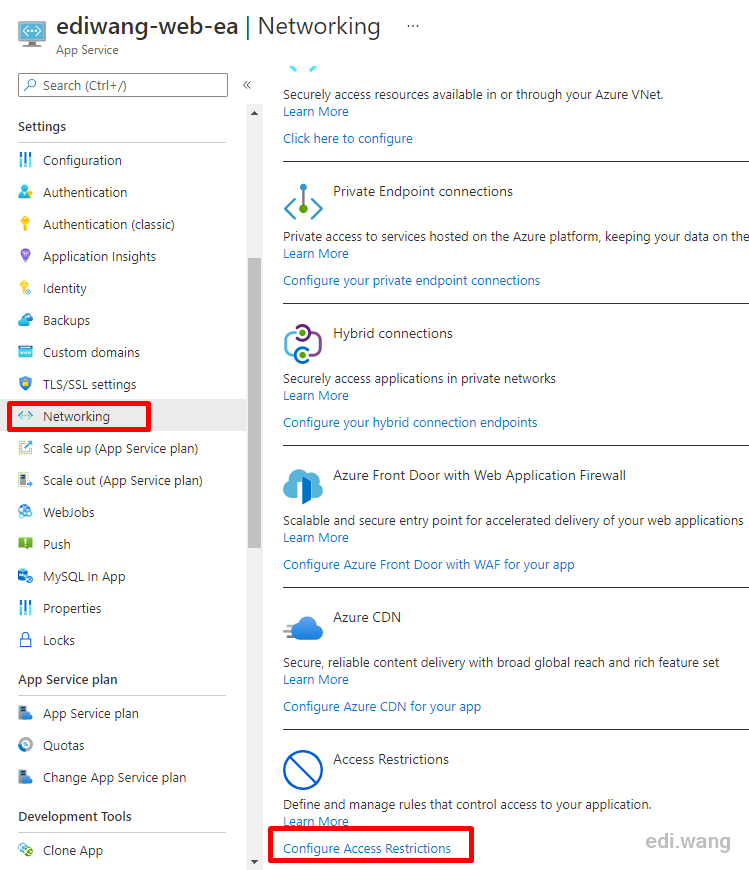
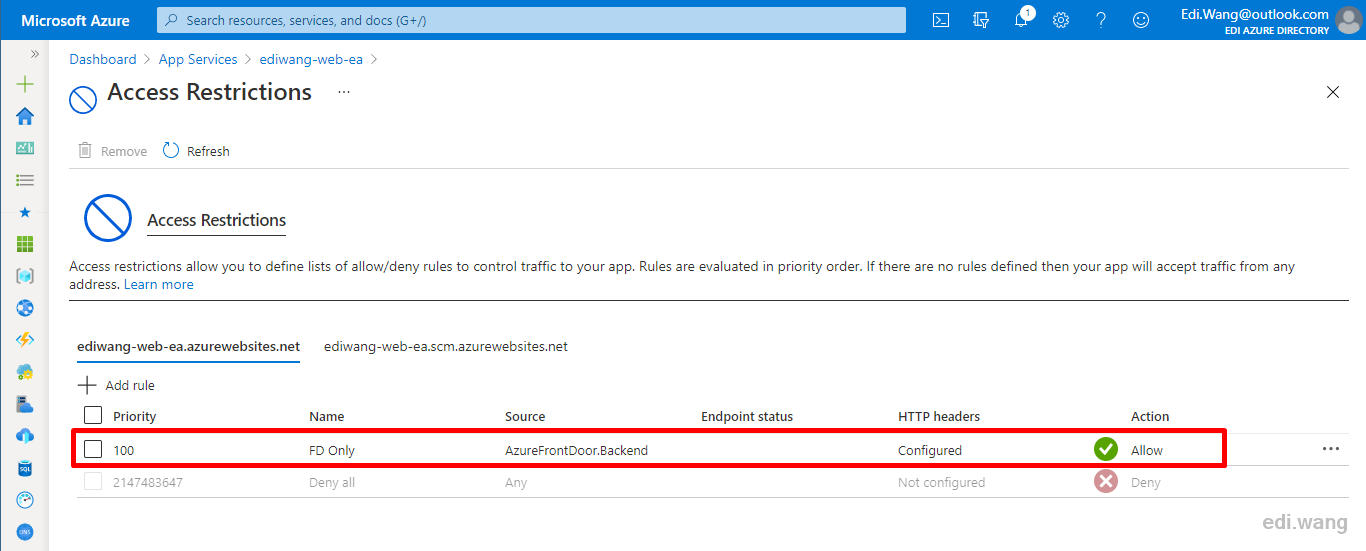
In your App Service management page, go to the "Networking" blade and click "Configure Access Restrictions".
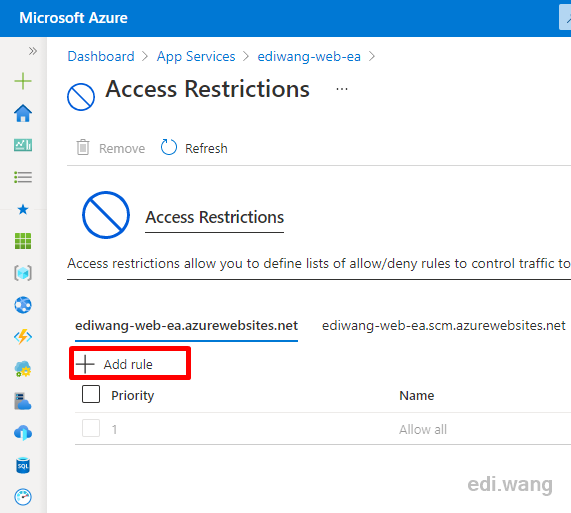
Find the DNS name that you don't want users to access. In my case, it's "ediwang-web-ea.azurewebsites.net".
Click "Add rule" button.
Give it a name and a priority you like. Choose "Service Tag" in Type, and select "AzureFrontDoor.Backend" as service tag.
You will also need to set the X-Azure-FDID header value.
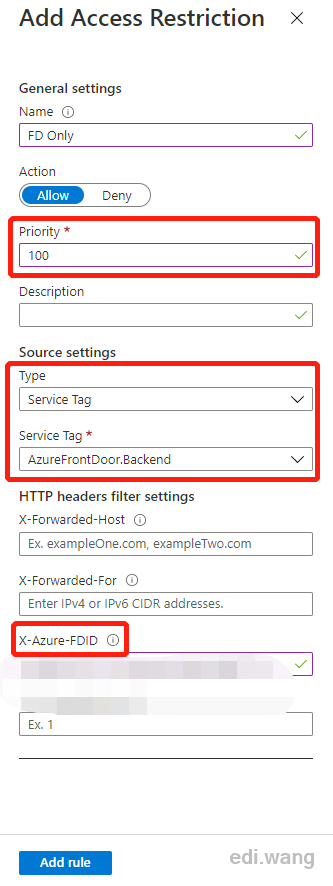
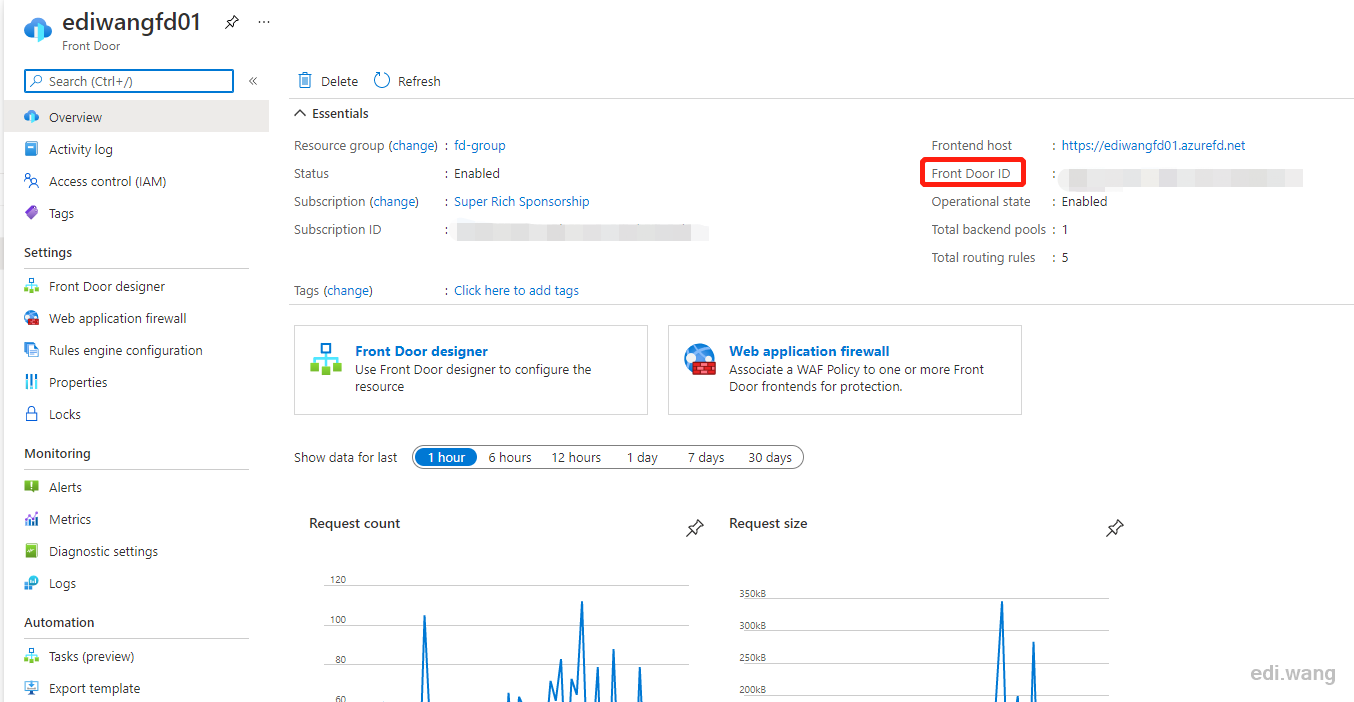
You can find the X-Azure-FDID value in your Front Door management page. It's in GUID format.
Save the rule, it will take effect immediantly.
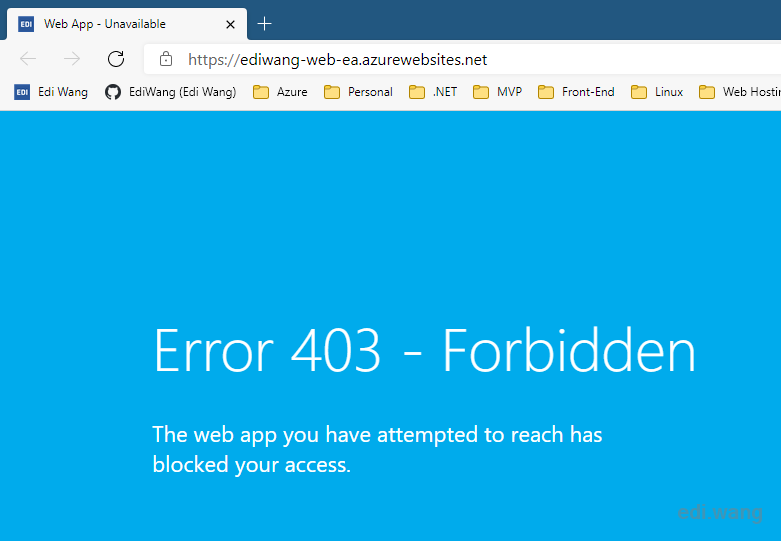
Now, try to access the App Service URL again, in my case, it's https://ediwang-web-ea.azurewebsites.net/
You'll now see a 403 result while access to https://edi.wang/ is still fine.
Do the same for every other backend pools, then you can restrict the user to visit your site only from Azure Front Door!
Kevin
Thank you! this prevented me from having to use azure ip block restrictions at the app service level as the best option and that wouldn't have been ideal at all!
Ihor
Thank you for the helpful article! It saved my time.
Bruno Santos
Thanks a lot Edi! Simplest way to solve my issue.